Many vulnerability scan results will show a Common Vulnerabilities and Exposures (CVE) code next to discovered vulnerabilities. The CVE code is a unique identifier assigned to a specific vulnerability of a particular product. This provides a standardized method for identifying and tracking vulnerabilities.
The format of a CVE code typically consists of the prefix “CVE-” followed by a year and a unique identifier number (e.g., CVE-YYYY-NNNN).
CVE codes are maintained and managed by the MITRE Corporation, a nonprofit organization. MITRE assigns CVE identifiers to reported vulnerabilities and maintains a public CVE database where information about vulnerabilities, including descriptions, impact assessments, and references, is made available. This database is located at https://cve.mitre.org/
To learn more about the vulnerability, simply click on the name, which will redirect you to the record in the National Vulnerability Database (NVD) and provide more detailed information on the vulnerability.
As vulnerabilities are identified, the severity is rated using the Common Vulnerability Scoring System (CVSS). The CVSS is developed by the Forum of Incident Response and Security Teams (FIRST) and has evolved through several versions, with the latest being CVSS 4.0. The score is derived using a set of metrics, which helps in prioritizing vulnerabilities. These metrics are divided into the following three groups:
-
Base - This metric represents the characteristics of a vulnerability that are consistent over time and across different environments. This metric is made up of two sub-metrics:
-
Exploitability - This metric reflects the difficulty required to exploit the vulnerability.
-
Impact - This metric reflects the direct consequence of a successful exploit.
-
-
Threat - This metric represents the characteristics of a vulnerability that do change over time, but not necessarily user environments.
-
Environmental- This metric represents the characteristics of a vulnerability based on the specific environment in which the vulnerability exists.
Supplemental- This metric provides additional information about the vulnerability, but doesn’t necessarily impact the final CVSS score.
CVSS Metric Groups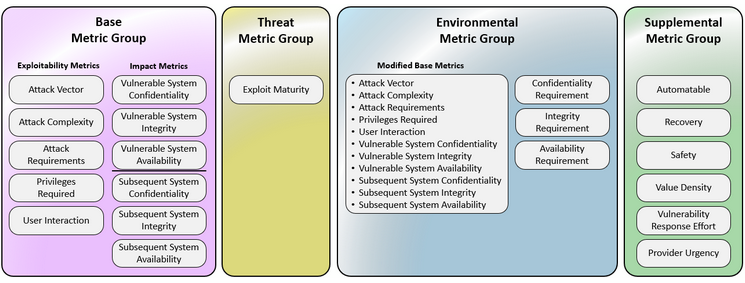
Copyright © 2025 by Forum of Incident Response and Security Teams, Inc.
Description
The image is a color-coded diagram illustrating the structure and components of different metric groups used in a vulnerability scoring system (such as CVSS v4.0). The diagram is divided into four sections from left to right:
- Base Metric Group which contains two categories:
-
Exploitability Metrics: Attack Vector, Attack Complexity, Attack Requirements, Privileges Required, and User Interaction.
-
Impact Metrics: Vulnerable System Confidentiality, Vulnerable System Integrity, Vulnerable System Availability, Subsequent System Confidentiality, Subsequent System Integrity, and Subsequent System Availability.
-
Threat Metric Group with one entry: Exploit Maturity
-
Environmental Metric Group which contains:
-
Modified Base Metrics (list): Attack Vector, Attack Complexity, Attack Requirements, Privileges Required, User Interaction, Vulnerable System Confidentiality/Integrity/Availability, and Subsequent System Confidentiality/Integrity/Availability.
-
Other requirements: Confidentiality Requirement, Integrity Requirement, and Availability Requirement.
- Supplemental Metric Group which contains: Automatable, Recovery, Safety, Value Density, Vulnerability Response Effort, and Provider Urgency.
These metrics are used to establish a final score for each vulnerability. Based on the score, the vulnerability threat will be classified in one of the following categories:
-
Low (0 - 3.9)
-
Medium (4 - 6.9)
-
High (7 - 8.9)
-
Critical (9 - 10)