Metasploit is the world’s most used open-source penetration testing framework, developed by Rapid7 and written in Ruby. It enables security professionals to find, exploit, and validate vulnerabilities in systems, networks, and applications. It provides a comprehensive, modular environment for running, testing, and developing exploit code to improve security posture.
Key features and components of Metasploit include:
MSFconsole: The main, most popular command-line interface used to access and manage Metasploit modules. Exploit Modules: Pre-written code that takes advantage of vulnerabilities to gain access to a target system. Payloads: Code that runs on the target system after successful exploitation, such as shells or Meterpreter, to control the system. Auxiliary Modules: Tools for scanning, reconnaissance, and sniffing network traffic. Automation: Capabilities for automating tasks like vulnerability scanning, password cracking, and maintaining persistent access.
It is widely used by ethical hackers (Red Teams) to simulate real-world attacks and by security defenders (Blue Teams) to test their defenses.
frameworks opensource exploits #tools tool vulnerabilityscanning reconnaissance payloads
Metasploit
Metasploit is a multipurpose computer security and penetration testing framework that is used worldwide for both legitimate security analysis and unauthorized activities. Developed by Rapid7, it is intentionally modular, as it allows the attacker to mix and match scanners, exploits, and payloads into a single attack. Metasploit currently comes in three editions:
- Metasploit Framework: The free open-source command-line version (installed by default in Kali Linux).
- Metasploit Express: A simplified commercial edition for security professionals who want to validate vulnerabilities.
- Metasploit Pro: A full-featured graphical version that includes quick start wizards, easy vulnerability scanning and validation, phishing campaigns, and reporting.
There are two popular GUI-based spin-offs:
-
Armitage: An intuitive GUI for Metasploit framework.
-
Cobalt Strike: A commercial version of Armitage with advanced features and reporting.
Metasploit’s features are organized into the following module types:
-
Exploit: Attack software that delivers a payload
-
Payload: Code that runs remotely
-
Post: Additional tasks that can be performed on a compromised host
-
Auxillary: Scanners, sniffers, fuzzers, spoofers, and other nonexploit features
-
Encoder: Ensures that payloads make it to their destination intact and undetected
-
Nop: Keeps payload sizes consistent across exploit attempts
Each type includes many modules, grouped by subtype or platform. Particular modules are specified by their path, as shown in the graphic below:
Outlining the path in Metasploit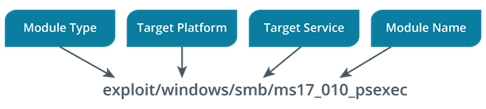 Description
Description
The image is a labeled diagram explaining the structure of a Metasploit module path, specifically using the example exploit/windows/smb/ms17_010_psexec.
-
The path is shown at the bottom in the format: exploit/windows/smb/ms17_010_psexec.
-
Four labeled blue boxes at the top break down each section of the path: Module Type → exploit, Target Platform → windows, Target Service → smb, and Module Name → ms17_010_psexec.
-
Arrows point from each box down to the corresponding word or section in the path.
-
The visual makes it clear how a typical Metasploit module path is composed—with each component specifying the module’s type, the platform it targets, the service on that platform, and the specific exploit or payload.
Metasploit allows the user to search for appropriate modules and exploits. Examples of searches include the following:
-
search EternalBlue type:exploit will search for all exploits that reference EternalBlue.
-
search Windows/MSSQL type:exploit will find exploits that can be used against Microsoft SQL running on Windows.
-
search Windows/SMB type:exploit -S great will list all Windows-based Server Message Block (SMB) exploits that have an excellent (most reliable) rating.