Wireless transmissions are sent through the air using a radio wave and are not protected by a bounded media, such as a cable. Any human or device within range and direction of the signal can intercept that signal without needing to access or disrupt a physical networking infrastructure. Some wireless technology, like Wi-Fi, is omni-directional— the intercepting entity does not have to face a specific direction, just be within range. Because of this, wireless networking technology is at a greater risk of compromise from several types of attacks.
Wireless communication is pervasive in today’s society. A wireless access point (WAP) enables devices to connect to a local network, typically using the 802.11 (Wi-Fi) standard. A WAP is an entry point into a network; it transmits data over the air to other devices and can be easily attacked. As a result, it is a worthwhile target to assess during the PenTest. A WAP’s susceptibility to compromise usually depends on the strength of its encryption scheme.
Wireless transactions sent and received on a LAN may contain sensitive information. For example, the connection in a coffee shop that offers free Internet might not be encrypted, which will leave users’ data exposed. A malicious actor might be able to obtain this data, which may include credit card numbers or login credentials, by using traffic sniffing. Because of this threat, it’s best to encrypt data with the strongest protocol available.
Several encryption protocols have been developed to protect wireless communications. The Wi-Fi Alliance is influential in providing guidance on wireless standards and has worked to improve each iteration in the evolution of security protocols.
Over the years, the predominant encryption standard, Wi-Fi Protected Access (WPA), has evolved to ensure improved protocols to secure wireless communication:
- WPA features the Temporal Key Integrity Protocol (TKIP). TKIP dynamically generates a new 128-bit key for each packet. In addition, WPA includes a Message Integrity Check (MIC), which provides a stronger method (than a cyclic redundancy check) to ensure data integrity.
- WPA2 is an improvement of WPA that replaced RC4 and TKIP with Counter Mode CBC-MAC Protocol (CCMP) using the Advanced Encryption Standard (AES).
- WPA3 includes advanced features to secure wireless transmissions such as 192-bit encryption when using WPA3- Enterprise mode (used in business LANs). It also features improved authentication, employs a 48-bit initialization vector, and uses Protected Management Frames (PMFs) to prevent exposure of management traffic.
Wi-Fi Discovery
Before a wireless network can be probed for vulnerabilities, it must first be discovered. The PenTester uses a process of discovery and footprinting to find the wireless network and obtain information that will help to breach it.
During Wi-Fi discovery, the scanning tool will scan for and report back the signal strength, channel, and Service Set ID (SSID):
-
The PenTester needs to pay attention to the signal strength. If the signal strength is too weak, they will have a difficult time testing the network, as packets can be dropped. Keep in mind that when measuring signal strength, dBm values closer to zero represent better performance. A value around -65 dBm represents a good signal, while anything over -80 dBm is likely to suffer packet loss or be dropped. It is not uncommon for the strength of a wireless network to fluctuate due to interference caused by physical structures or other nearby devices and wireless networks.
-
Once the wireless network has been discovered, the PenTester should verify the channel that the wireless network is operating on. Channel scanning is a process that assists in identifying which wireless channels are being used by the different wireless networks. Many of the wireless scanning and hacking tools, such as airmon-ng, will allow the PenTester to specify the channel to listen and capture packets on. Specifying the channel will reduce the workload of the wireless scanner.
-
The Service Set ID (SSID) is the name of the wireless network. Some wireless scanning tools will be able to resolve and display the SSID even if it is supposed to be hidden.
Two of the most important things needed to break into a wireless network are the Basic Service Sets (BSS) and the SSID. Both of these are provided by access points. The process of Wi-Fi discovery can be either passive or active:
-
Passive Wi-Fi discovery uses a wireless listening device, known as a sniffer, to capture packets in an attempt to discover the critical information needed. This is often done using the wardriving method, where the hacker drives around with a wireless laptop and external Wi-Fi antenna, trying to locate wireless networks. With passive footprinting, no attempt is made to connect with any of the access points or wireless clients. The PenTester is only collecting data.
-
Active Wi-Fi discovery uses information obtained from the passive technique to get a little more aggressive in the attack on the network. For example, the PenTester can send packets to the access point using a discovered SSID or send a probing packet without the SSID. When a probing packet without an SSID is answered, it includes the BSS.
Exploiting the Four-Way Handshake
Once a wireless network has been discovered, the PenTester can attempt to intercept the four-way handshake that occurs when a device attempts to connect to the wireless network. The pre-shared key and SSID are used to generate a session key during this process.
-
First, the access point sends a clear text challenge, which is a randomly generated number.
-
Next, the client encrypts the challenge text using the preconfigured pre-shared key and sends it back to the access point in another authentication request.
-
The access point decrypts the material it receives and compares it with the clear text it sent in the first place. If the decryption process was accurate and the text is correct, the access point will send back a positive response along with another shared key.
-
The client verifies everything and, if it all matches, sends an acknowledgment to the access point and the connection is established.
Four-Way Handshake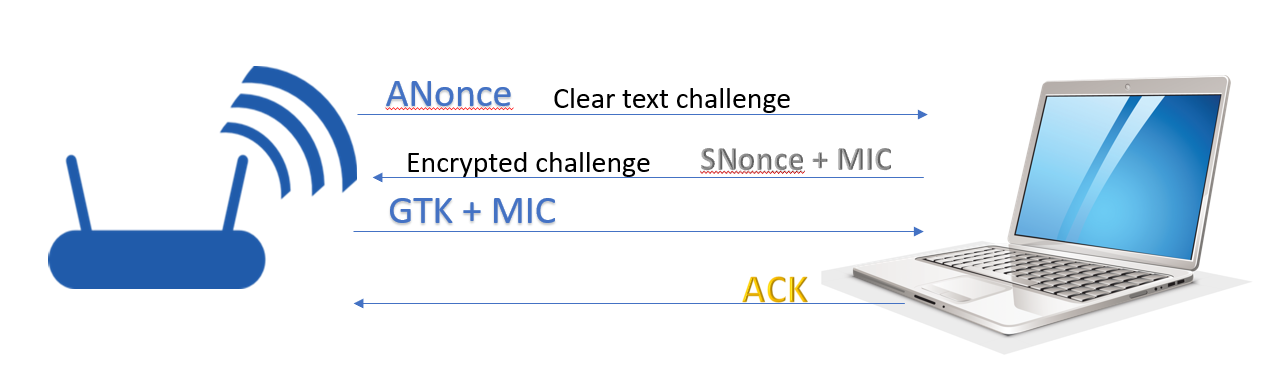 Description
Description
Image of the WPA/WPA2 4-way handshake process used in Wi-Fi security between a wireless router (on the left) and a laptop (on the right). The sequence of message exchanges is shown as arrows directed between these two devices, each arrow labeled with its content and message type:
-
An arrow from the router to the laptop labeled “ANonce Clear text challenge”: This is the first message, where the router sends a random value (ANonce) to the client (laptop) as a clear text challenge.
-
An arrow from the laptop to the router labeled “Encrypted challenge SNonce + MIC”: The laptop responds with its own random value (SNonce) and a Message Integrity Code (MIC), in an encrypted form.
-
An arrow from the router to the laptop labeled “GTK + MIC”: The router sends the Group Temporal Key (GTK) and another MIC to the laptop.
-
An arrow from the laptop back to the router labeled “ACK”: The laptop sends an acknowledgment (ACK) to confirm successful reception and completion of the handshake.
Using tools such as airmon-ng, the PenTester can intercept the handshake and then attempt to crack the password offline. Once this key is discovered, the PenTester can easily connect to the wireless network legitimately.
vulnerabilityscanning scanning WirelessSecurity wifihacking overview