Secrets scanning involves scanning assets for sensitive information. Secrets can include data such as the following:
-
Credentials
-
Cloud access keys
-
Encryption keys
-
Configuration data
When performing secrets scanning, the PenTester will typically scan the following areas:
-
Code repositories such as GitHub, which are used by developers to store source code for applications and services
-
Configuration files used by applications or infrastructure components, which will often have secrets stored in them
-
Log files and metadata, which may contain secrets
-
Other assets such as scripts and internal documentation that may also contain secrets
The PenTester can of course manually scan through these resources to discover secrets, but using an automated tool will make this process much easier. One tool that can assist in this process is TruffleHog.
TruffleHog
TruffleHog is designed to scan through code repositories, Docker images, ticket systems, and more to discover secrets. It can be installed and run from Windows, MacOS, or Linux-based systems.
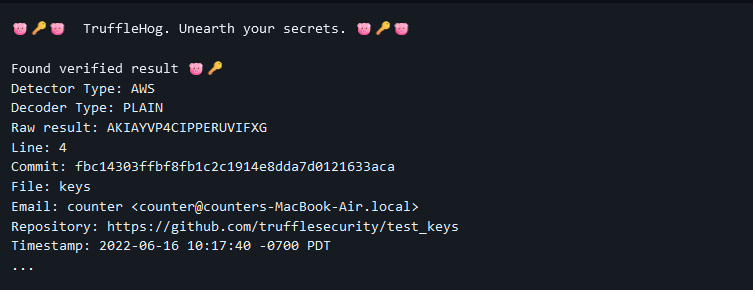
Once installed, the PenTester simply runs the program and specifies what needs to be scanned, and TruffleHog will comb through the system and list any discovered secrets, as shown in the below screenshot:
TruffleHog Results